AppWall – More Than Just a WAF

As cyberattacks and mitigation techniques continue to evolve, enterprises need to be on alert and keep time to protection as short as possible. Advanced methods
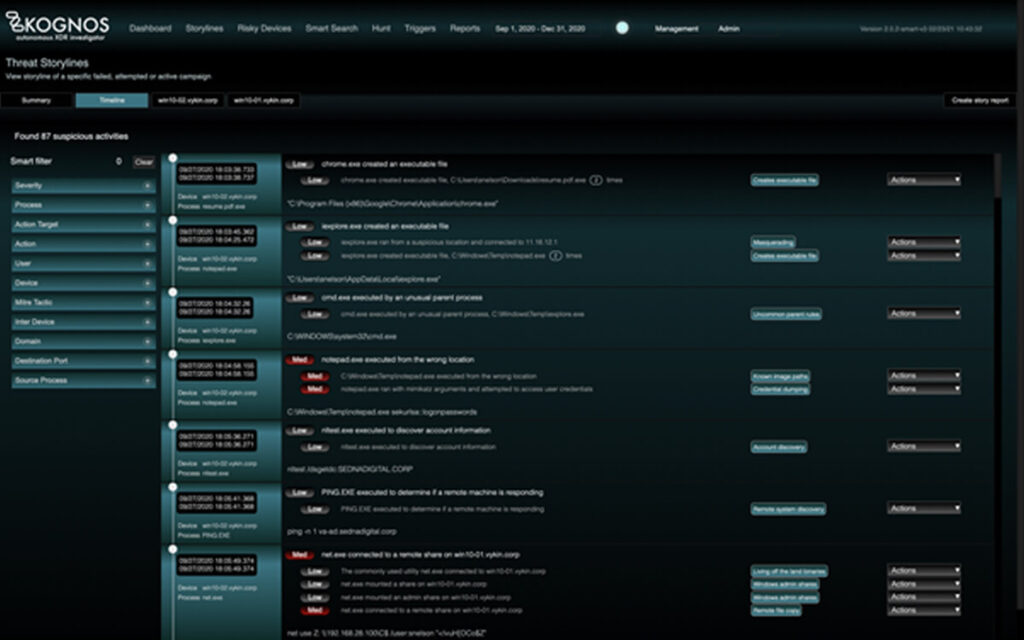
Do You Still Need An MDR? (Part 3/3)
IDENTIFY ATTACKERS IN ACTION Attackers are becoming more sophisticated and the techniques they use are much stealthier, harder to detect, and take increasingly longer to
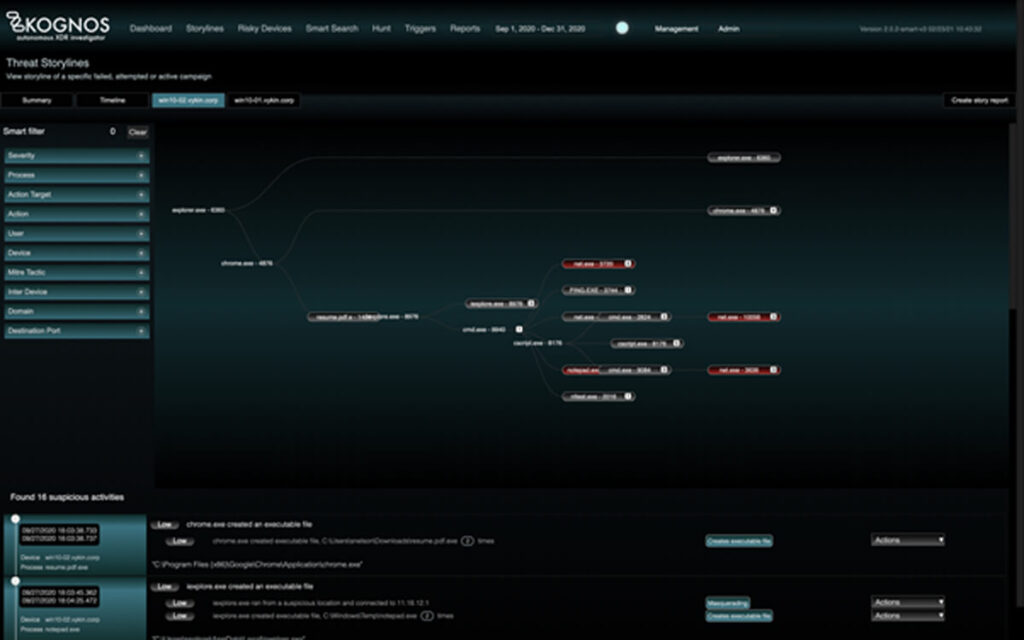
Do You Still Need An MDR? (Part 2/3)
IDENTIFY ATTACKERS IN ACTION Attackers are becoming more sophisticated and the techniques they use are much stealthier, harder to detect, and take increasingly longer to
Do You Still Need An MDR? (Part 1/3)
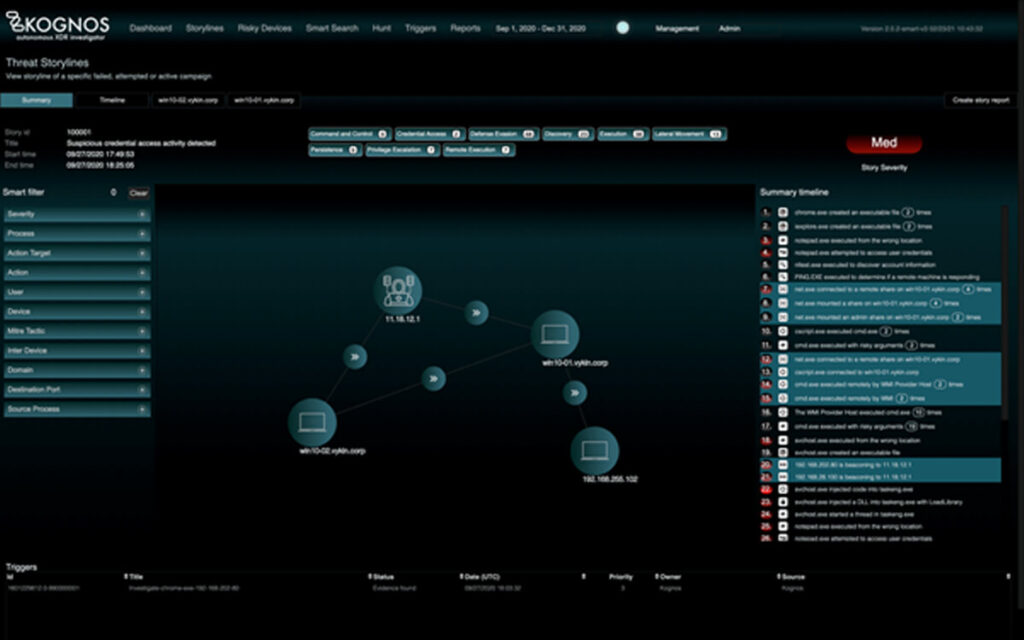
IDENTIFY ATTACKERS IN ACTION Attackers are becoming more sophisticated and the techniques they use are much stealthier, harder to detect, and take increasingly longer to
Life With an XDR Without The Understanding of Relationship Centric Approach to Threats

The introduction of XDR is a major evolution in understanding the effectiveness to threats within an organization. The threat data is available to Security analysts


